This software is not designed for, and we do not encourage:
- Concealing criminal activity
- Evading lawful, narrowly-tailored court orders served on the user
- Defeating sanctions screening at regulated counterparties
- Hiding from legitimate journalism, public oversight, or accountability
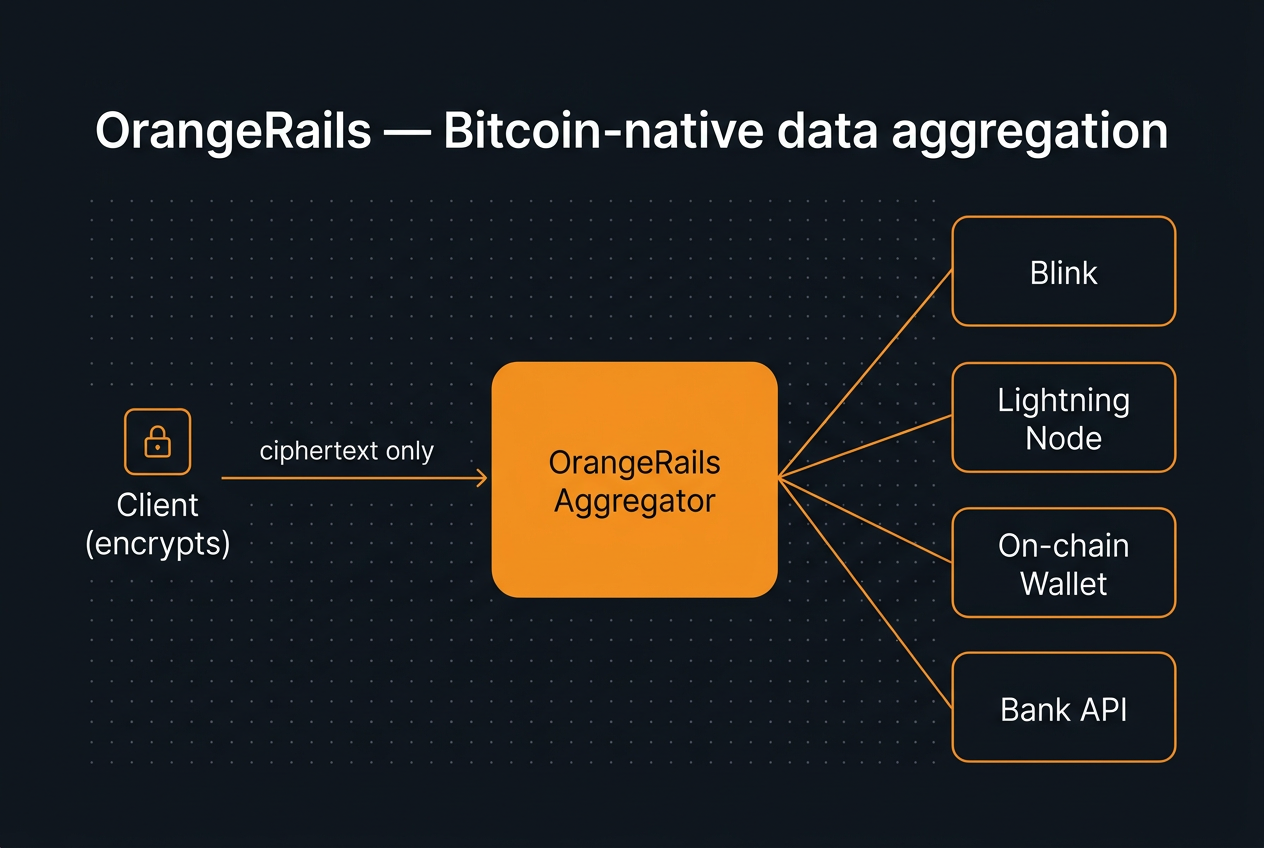
If a court has a lawful warrant, it can serve it on the user — who has rights, due process, and the option of legal counsel. The operator does not have those protections, and zero-knowledge architecture means the operator does not have the data either.
What we object to is the asymmetric default: that every operator becomes a surveillance target before any specific case exists, and that hundreds of millions of records sit in plaintext as a permanent target waiting for a subpoena, a breach, an acquisition, or a regime change.